TL;DR
- Terraform Cloud uses per-resource billing for every resource present in your state file (including small or generated resources), which is counted and billed hourly.
- Costs of using Terraform Cloud grow linearly with scale, reaching thousands of dollars per month at 20K+ resources, even for teams with modest infrastructure.
- Lower pricing tiers come with hard constraints, limited concurrent Terraform runs, minimal policy enforcement, and no built-in drift detection or cost mapping.
- Platform teams often adopt workarounds, writing wrappers, tracking drift manually, or using external tools to compensate for visibility and governance gaps.
- IaC orchestration platforms like Firefly provide flat-rate pricing and built-in visibility without requiring changes to existing Terraform code or workflows.
Terraform Cloud has become the default starting point for many teams adopting infrastructure as code. It takes care of remote state storage, locking, and provides a CI/CD-like pipeline for running plans and applies. It’s clean, it works well, and it's backed by HashiCorp, so it feels like the safe choice.
But once your infrastructure scales beyond a handful of environments and modules, you quickly start to hit limits, not technical limits, but pricing and governance constraints that directly affect how platform teams operate day-to-day.
The pricing model changed recently to what HashiCorp calls Resource Under Management (RUM). This means you now pay per resource managed by Terraform Cloud, and the definition of "resource" is as granular as it gets. Every subnet, security group rule, EBS volume, or autoscaling policy is a billable item. This pricing model sounds simple, but once you do the math across environments like dev, staging, and production, it becomes hard to predict and even harder to justify.
For many teams, that’s added real cost pressure. In one widely discussed Reddit post, a user calculated their Terraform Cloud bill jumping from $0 to over $15,000 per year, mostly due to lightweight GraphQL mappings being priced the same as full cloud services.
This post walks through how Terraform Cloud pricing actually works, where it starts to pinch, and how tools like Firefly can help fill the visibility and governance gaps, without forcing a full platform migration.
Why Terraform Cloud No Longer Charges per User?
In mid-2023, Terraform Cloud switched from its long-standing user-based pricing model to one based on Resources Under Management (RUM). This wasn't a minor adjustment; it fundamentally changed how platform teams need to plan, model, and pay for infrastructure at scale.
Before this shift, costs were tied to how many people used Terraform Cloud. Now, costs scale with how many cloud resources Terraform manages, regardless of team size, activity, or actual cloud spend.
What Terraform Cloud’s Pricing Looked Like (Before IBM’s acquisition)
Before Terraform Cloud moved to metered, per-resource billing, pricing was based on the number of users in an organization, not the infrastructure being managed. Here’s how:
- The Free Tier included up to 5 users, basic VCS support, and shared state.
- The Team Tier was priced at $20/user/month, offering workspace permissions and team management.
- Business and Enterprise tiers were custom-priced, typically adding SSO, audit logs, and private runners.
Under this model, a team of 4 engineers could manage thousands of resources and pay the same flat rate every month; the infrastructure size didn’t affect billing.
What Changed With RUM-Based Billing
After the change, Terraform Cloud began billing based on the number of managed resources. These include:
- Every compute, network, storage, and IAM object in your .tfstate
- Generated resources like aws_security_group_rule, google_project_iam_binding, or Kubernetes workloads
- Even low-impact objects like CloudWatch alarms, DNS records, or GitHub webhooks
All of these are counted equally. There’s no distinction between small and large resources, and there’s no pricing relief for modular or multi-env setups. Terraform Cloud now meters resources hourly, across all active workspaces. Even short-lived dev or CI environments are billable while they exist.
Current Terraform Cloud Pricing (2026)
How Resource-Based Billing Affects Infrastructure Design and Operations
This new model doesn’t just raise costs; it changes how infrastructure needs to be managed.
- Modular infra costs more: Using granular modules or provider-generated resources (like IAM bindings or SG rules) inflates your bill, even though it’s good engineering practice.
- Environment sprawl becomes expensive: Dev/stage/prod copies triple your resource count. Add feature branch environments or CI preview stacks, and the meter runs constantly.
- Concurrency limits become real blockers: Even paid tiers have caps. Standard gives you just 3 concurrent runs, not enough for large teams with parallel pipelines or frequent PR-based deployments.
- Policy enforcement is paywalled: You don’t get meaningful Sentinel policy enforcement unless you’re on Premium or Enterprise. Standard gives you just 5 policies, with only 1 enforceable.
Post-IBM: Where Pricing Stands Now
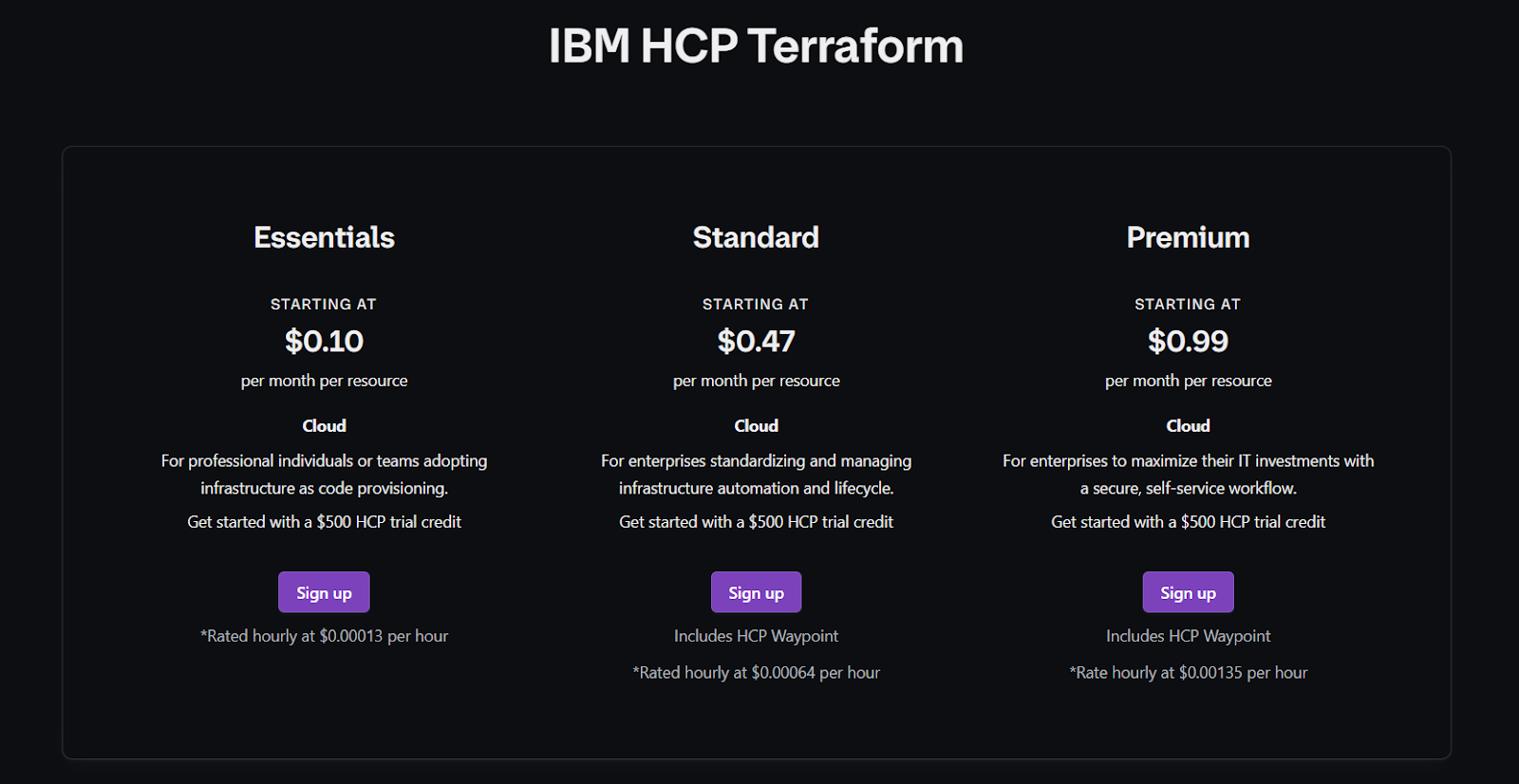
IBM finalized its acquisition of HashiCorp in early 2025. Since then, Terraform Cloud (now officially branded HCP Terraform) has continued down the enterprise-first path:
- The Free Tier is being phased out for many orgs by early 2026
- Pricing remains usage-based, with no flexibility around types of resources or environment strategy
- Long-term commitments are being pushed, especially for Premium and Enterprise tiers
So far, there’s no indication that pricing will return to a flat or tiered model; all signs point to tighter metering and higher predictability for HashiCorp’s revenue, not yours.
How to avoid Terraform Cloud Cost Spikes?
If you're managing infrastructure across multiple environments, clouds, or business units, you need to:
- Track your actual resource count per workspace and per environment
- Forecast cost impact for new modules or planned environment duplication
- Avoid patterns that generate high resource cardinality (like per-rule SGs or dozens of IAM bindings)
- Prepare for limited policy and concurrency unless you budget for Premium+ tiers
The move to RUM wasn’t just a pricing change; it redefined what Terraform Cloud is optimized for. Teams that don’t adapt end up constrained by concurrency, surprised by billing, and stuck without visibility into how their infrastructure is growing.
What Terraform Cloud Really Costs Across 5K, 25K, and 100K Resources
Terraform Cloud’s Resource-Under-Management (RUM) billing charges for every managed object recorded in Terraform state. That includes top-level resources (EC2, RDS, GKE clusters) and provider-generated children (security-group rules, IAM bindings, Helm/chart subresources, data-source mappings). Metering is hourly; monthly cost = per-resource monthly rate × number of managed objects.
Rates used in these examples (published list rates):
- Essentials: $0.10 / resource / month to ≈ $0.00013889 / resource / hour (0.10 / 720)
- Standard: $0.47 / resource/month to ≈ $0.00065278 / resource/hour
- Premium: $0.99 / resource/month to ≈ $0.00137500 / resource/hour
Below are three concrete scenarios showing typical infra, exactly what gets counted, the math, and operational notes you can act on.
Scenario A: ~5,000 managed resources
Setup: Small platform team (2 engineers). Single cloud account. Three environments (dev/stage/prod). Modular infra: VPCs, subnets, ALBs, IAM roles, a few services, and some preview workspaces.
Representative breakdown (one plausible split):
- Networking (VPCs, subnets, route tables, IGW): ~600
- Compute & autoscaling (ASGs, launch templates, ALBs): ~900
- IAM (roles, policies, instance profiles): ~450
- Storage & DB (S3, EBS, RDS): ~350
- Monitoring (alarms, log groups): ~200
- Provider objects (GitHub repos/webhooks, small K8s objects): ~200
- Module duplication across envs: ~1,300
- Other shared infra & housekeeping: ~1,000
Total ≈ 5,000 objects
Monthly cost:
- Essentials: 5,000 × $0.10 = $500 / month
- Standard: 5,000 × $0.47 = $2,350 / month
- Premium: 5,000 × $0.99 = $4,950 / month
Operational notes:
- Essentials provides almost no governance and 1 concurrent run, while Standard provides 3 concurrent runs. If your CI spikes to >3 parallel applies, expect queueing and slower PR feedback.
- Small actions (adding a module, adding a couple of IAM bindings) can create hundreds of billable objects, and audit the state before making changes.
Scenario B: ~25,000 managed resources
Setup: Mid-size SaaS org. Multi-region AWS + some GCP. 8–12 engineers. Full PR preview stacks enabled (per-PR environments), heavy use of Kubernetes operators, and many small provider objects (IAM bindings, DNS records, alert rules).
Representative breakdown:
- Shared infra & global networking: ~3,500
- Service infra (many microservices across regions): ~8,000
- Kubernetes & Helm/operator objects: ~4,000
- IAM fine-grained bindings: ~2,500
- Storage + DBs + snapshots: ~1,500
- Monitoring + dashboards + alerts: ~1,500
- Active previews / ephemeral envs (average live footprint): ~2,000
- Misc provider children: ~1,000
Total ≈ 25,000 objects
Monthly cost:
- Essentials: 25,000 × $0.10 = $2,500 / month
- Standard: 25,000 × $0.47 = $11,750 / month
- Premium: 25,000 × $0.99 = $24,750 / month
Ephemeral preview example:
- Assume average preview = 300 objects, active 6 hours.
- Standard hourly rate = $0.00065278 / obj/hr
- Cost per preview = 300 × 0.00065278 × 6 ≈ $1.17
- 200 previews/month ≈ $234 / month just from previews.
Operational notes:
- Preview stacks and operator child resources are the biggest hidden drivers. Standard’s 3 concurrent runs is frequently insufficient for many teams, which pushes them to Premium or alternative orchestration.
- Policy enforcement on Standard is very limited (5 policy checks, 1 enforceable), so governance often requires additional tooling or an upgrade.
Scenario C: ~100,000 managed resources
Setup: Large enterprise. Many business units, multi-cloud, dozens of teams. Per-service IAM bindings, multiple clusters with operators, frequent Helm releases, and heavy ephemeral usage for testing and CI.
Representative breakdown:
- Global/regional networking: ~12,000
- Microservice compute infra: ~35,000
- K8s operator + Helm children: ~20,000
- IAM / SSO / bindings: ~10,000
- Storage / DBs / backups: ~8,000
- Monitoring/dashboards: ~5,000
Total ≈ 100,000 objects
Monthly cost:
- Essentials: 100,000 × $0.10 = $10,000 / month
- Standard: 100,000 × $0.47 = $47,000 / month
- Premium: 100,000 × $0.99 = $99,000 / month
Operational notes:
- At this scale, teams typically negotiate Enterprise pricing, move to self-hosted execution, or adopt additional control planes. Hidden costs to include in TCO: run-queue delays, engineering time for homegrown drift detection, and cost of multiple point tools.
- Helm/operator churn plus per-service IAM patterns are the most common amplifiers of RUM counts.
Short-Lived Environments and Hourly Metering
Terraform Cloud meters resources hourly. Even stacks spun up for just a few hours contribute to your bill.
Example:
- 250-resource preview environment
- Active for 8 hours
- Essentials rate: $0.10 / month, ~$0.00014 / hour
- Cost = 250 × 0.00014 × 8 = $0.28 per preview
Multiply this by dozens of PRs per week, and ephemeral usage becomes a meaningful part of your monthly cost.
Challenges for Platform Teams Using Terraform Cloud at Scale
As infrastructure grows, Terraform Cloud introduces more than just cost increases. Its pricing model directly affects how teams structure workflows, manage environments, and enforce standards. Below are key challenges that emerge as platform usage expands.
1. Cost Unpredictability
With per-resource billing, it’s hard to forecast Terraform Cloud spend unless you actively track resource counts across all environments and workspaces. Even minor architectural changes, like adding new modules, enabling a monitoring agent, or updating tagging policies, can inflate your state file by hundreds of resources.
If you’re managing multiple environments (dev/staging/prod) or replicating stacks for PR previews, cost modeling becomes a moving target. Since resources are metered hourly, even temporary stacks contribute to your monthly usage.
2. Run Concurrency Limits
Concurrency is tier-bound and caps out quickly:
- Essentials: 1 concurrent run
- Standard: 3 concurrent runs
- Premium: 10 concurrent runs
For teams using Terraform in CI pipelines or multi-region deploys, this becomes a major bottleneck. Applies get queued, PR feedback slows down, and long-running plans block others. In large orgs, run queue latency turns into real productivity loss.
Unless you’re on Enterprise with self-hosted agents, there’s no native way to scale this horizontally.
3. Governance Gaps on Lower Tiers
Sentinel policy enforcement, Terraform Cloud’s mechanism for codifying compliance and security controls, is mostly locked behind higher tiers.
- Standard only allows 5 policies, with 1 enforceable
- Essentials has no policy enforcement at all
- Premium unlocks full Sentinel policy usage and role-based access controls (RBAC)
Teams needing even basic guardrails (e.g., required tagging, region restrictions, cost limits) have to jump to Premium or build homegrown checks outside Terraform Cloud entirely.
4. Limited Visibility Into Infrastructure State and Drift
Terraform Cloud doesn’t provide any built-in tools for:
- Detecting drift between the actual cloud state and the declared IaC
- Identifying unmanaged (out-of-band) changes
- Mapping resource cost or usage back to Terraform modules
Teams are left to build their own tooling or bolt on external scripts to handle this, often with unreliable results and high engineering effort.
At scale, not having visibility into infrastructure health, drift, or cloud waste creates both operational and compliance risks.
5. High Operational Overhead for CI/CD Scaling
Without sufficient concurrency or governance baked in, many teams build custom wrappers to orchestrate runs, enforce policies, and manage workspace sprawl. That leads to:
- Fragile custom tooling
- Duplicated logic across repos
- Inconsistent enforcement across teams
- Poor observability into what's happening across environments
The effort required to manage this friction grows with each new service, team, or environment introduced
Hitting Limits With Terraform Cloud’s Resource-Based Pricing
As resource counts grow, platform teams eventually run into Terraform Cloud’s hard constraints, not just in pricing, but in how the system handles concurrency, governance, visibility, and scale. These limits impact daily workflows and create architectural friction as teams attempt to scale usage across services, environments, and clouds.
Pricing That Doesn’t Scale With Usage Type
Terraform Cloud’s RUM pricing doesn’t differentiate between resource types or use cases. That means:
- A single aws_security_group_rule costs the same as a production-grade aws_rds_instance
- Preview environments for dev branches incur the same per-resource cost as long-lived production stacks
- Even data-only resources (e.g., GitHub teams, dashboards, IAM bindings) are metered just like compute
This pricing model penalizes modular design, multiple environments, and dynamic infra patterns, all of which are standard for platform teams. Cost grows with infrastructure complexity, not value delivered.
Concurrency Bottlenecks Show Up Early
Even moderately sized teams hit Terraform Cloud’s run queue limits. Three parallel CI pipelines deploying across regions or accounts are enough to max out concurrency under Standard. After that, the plans queue until another finishes.
This forces teams to:
- Serialize deployments
- Split stacks more aggressively (increasing overhead)
- Limit automation or schedule pipelines to avoid contention
Unless you’re on Premium or Enterprise with self-hosted runners, these concurrency walls are unavoidable.
Limited Governance Without Paying Up
Most security-conscious teams need guardrails: required tags, blocked services, region restrictions, budget caps, etc. But Sentinel policies are locked down unless you're on Premium or Enterprise.
On Standard:
- Only 5 policies total
- Only 1 can be enforced (the rest are advisory)
This creates gaps in enforcement; policies that can't block violations don't prevent drift, misconfigurations, or cost leaks. For most teams, this means either paying more, building external policy engines, or hoping advisory rules are followed.
Tooling Fragmentation Starts to Creep In
To plug these gaps , cost visibility, drift detection, resource tagging compliance , teams start reaching for separate tools: Bash wrappers, cost analysis scripts, tagging audits, drift scanners, internal dashboards, and more.
Each one works for a narrow slice of the problem, but none are unified. Over time:
- Infra workflows slow down
- Engineers lose confidence in what Terraform is managing
- Platform ownership gets diluted across scripts and teams
This fragmentation happens not because Terraform doesn’t work, but because Terraform Cloud doesn’t give platform teams the levers they need unless they move to top-tier plans.
By the time a team hits 10,000+ resources, or runs more than a few concurrent applies in CI/CD, these limitations are no longer theoretical. They affect how quickly services can ship, how consistently infrastructure is enforced, and how efficiently cloud cost is managed.
This is where Firefly can be used as an alternative, offering infrastructure visibility, drift detection, policy enforcement, and cost insights without per-resource pricing.
How Firefly Solves Terraform Cloud’s Scaling and Cost Challenges
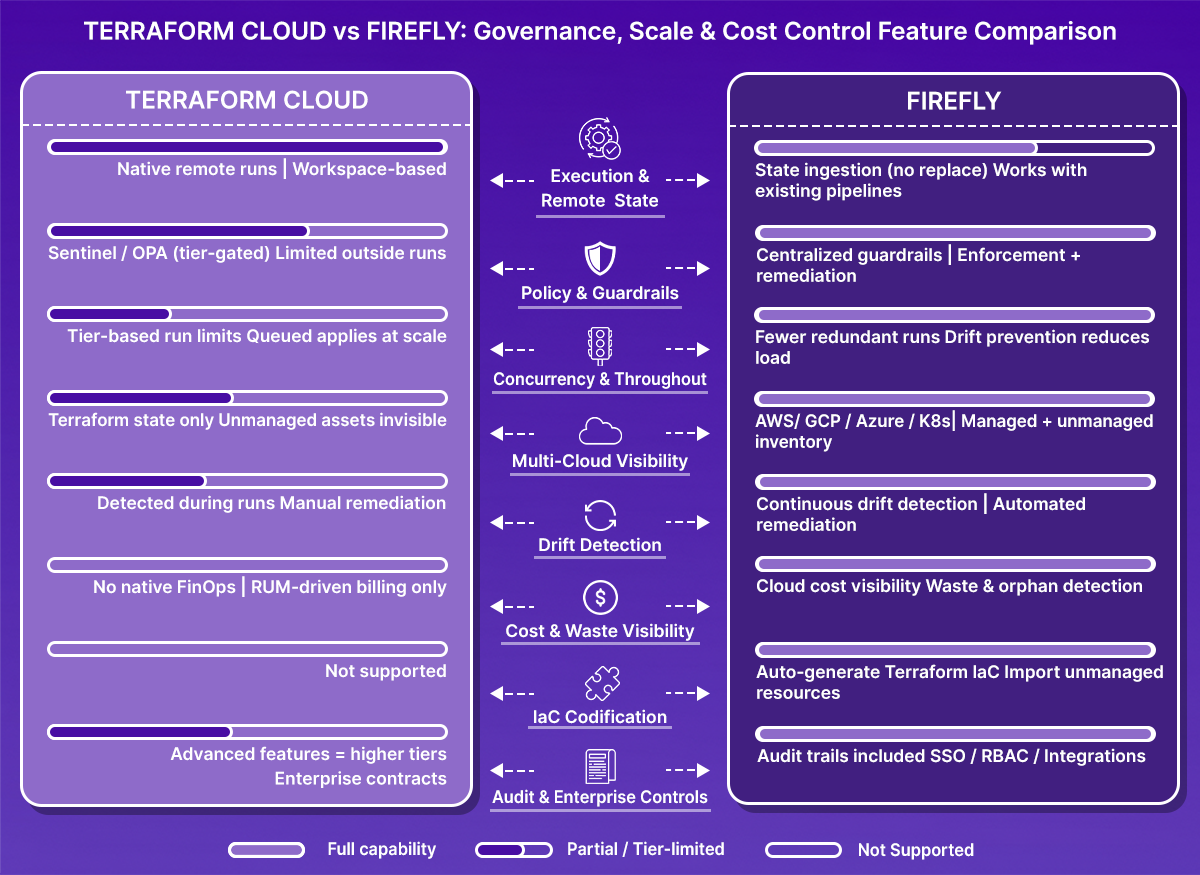
As teams scale infrastructure across multiple environments, accounts, and cloud providers, Terraform Cloud’s resource-based pricing and feature gating can introduce friction. Firefly offers an alternative approach by providing a unified control plane for infrastructure management, with flat-rate pricing and built-in visibility, drift detection, and governance.
Firefly integrates directly with Terraform, including Terraform Cloud and Enterprise, by ingesting existing state files. It doesn’t require changing the IaC structure or rewriting modules. Once connected, it continuously maps infrastructure state, highlights drift, enforces policies, and helps teams optimize cost and resource sprawl.
Terraform Cloud Integration Example
Once Terraform Cloud is connected to Firefly, remote states are automatically ingested and monitored. Teams can view each workspace and manage the integration directly. As shown in the snapshot below, a connected Terraform Cloud workspace inside Firefly.
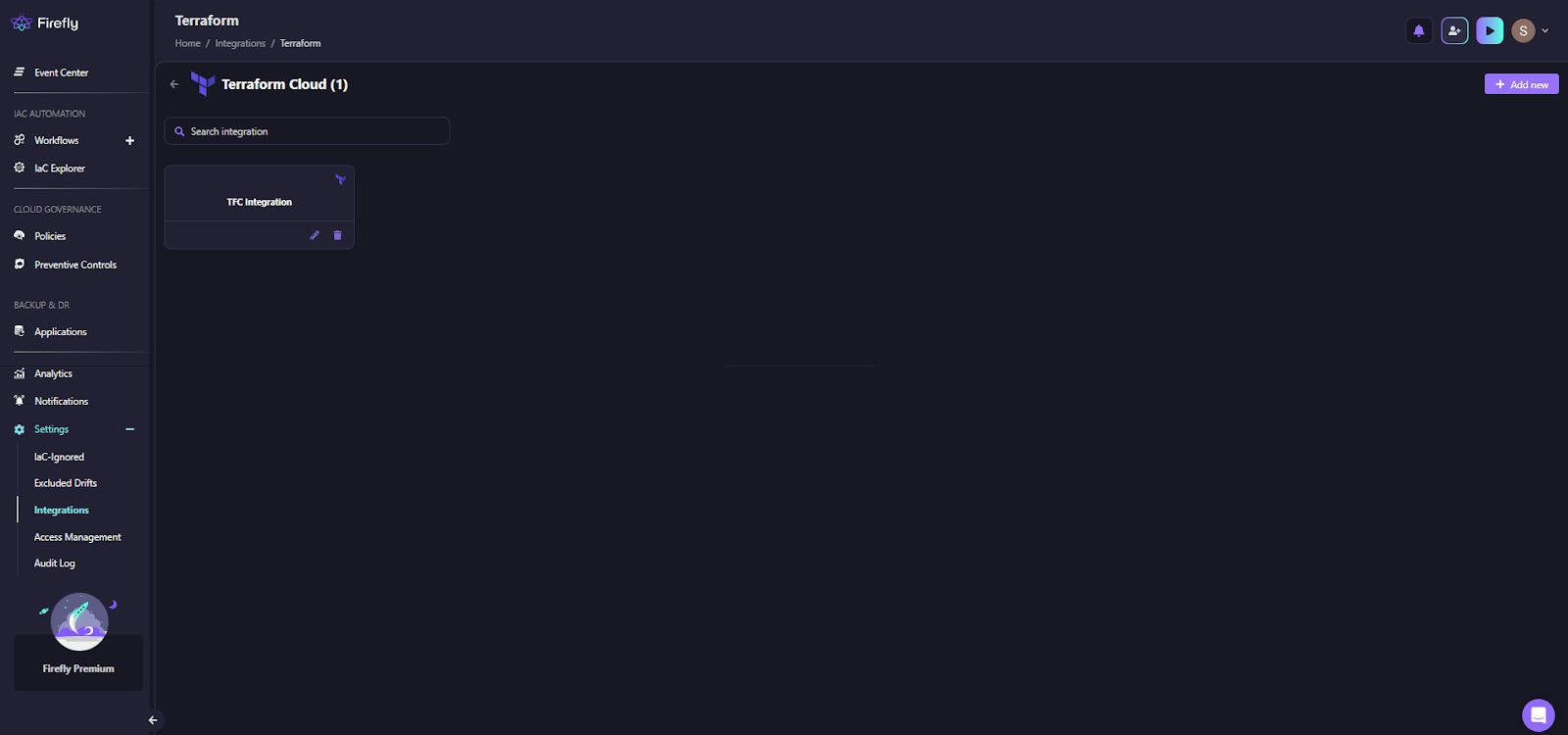
Teams can ingest state files and begin visibility workflows without altering existing Terraform code.
Cross-Cloud Inventory and IaC Classification Example
Firefly builds a unified inventory across all cloud providers, classifying each resource as codified, drifted, or unmanaged. This helps identify inconsistencies, policy violations, and unused infrastructure across projects, all from a single interface. As shown in the snapshot below:
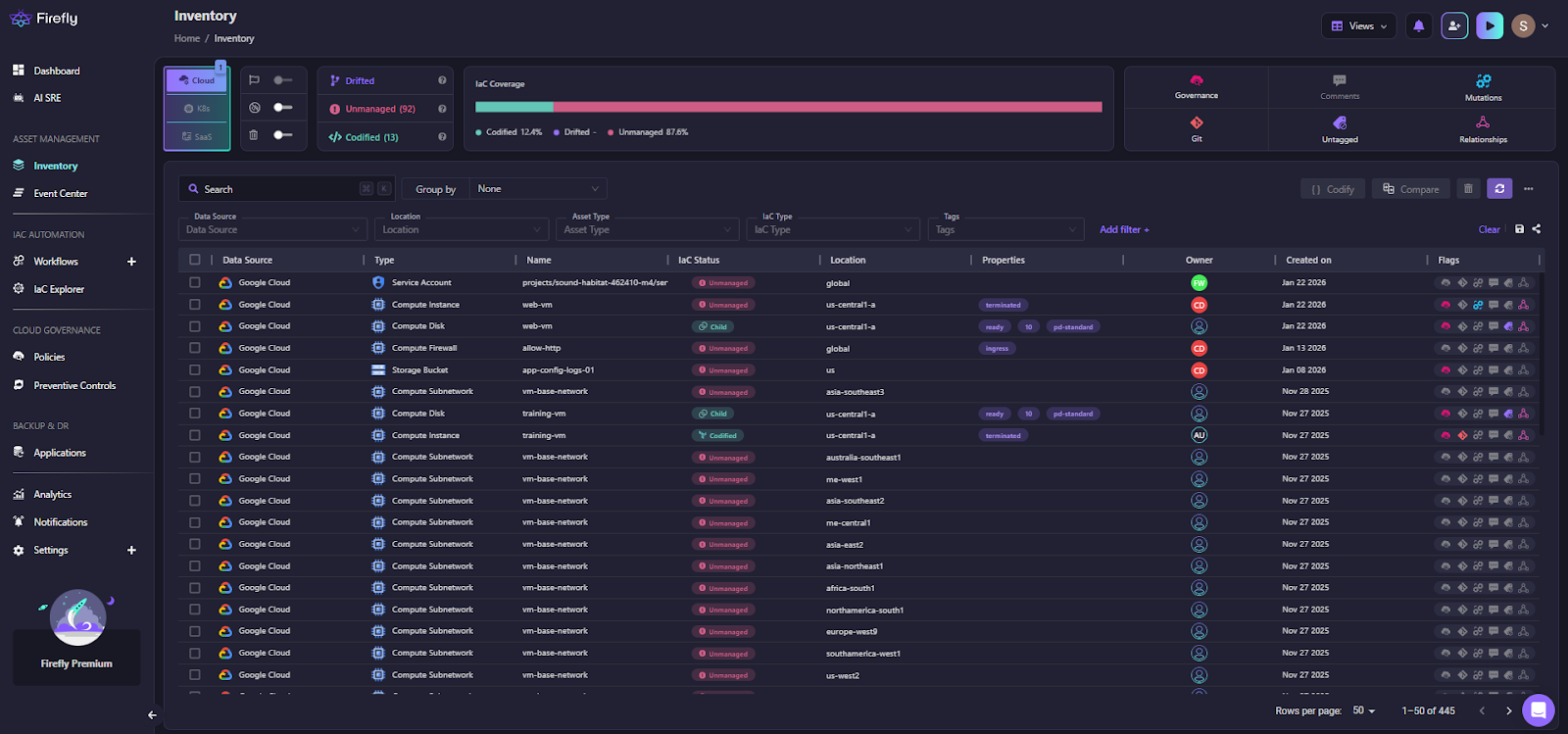
Firefly’s inventory view showing Google Cloud resources classified by resource type, drift status, and location. This view gives teams a quick way to track IaC coverage and pinpoint cost and compliance risks.
Feature Comparison: Firefly vs. Terraform Cloud
Cost Comparison: Firefly
At smaller scales, Terraform Essentials remains the most economical option, but it provides limited visibility, governance, and enforcement capabilities.
As usage grows to around 25,000 resources, Firefly’s flat pricing becomes cost-comparable. At this point, Firefly delivers significantly more value through built-in governance, drift detection, and cost-optimization features.
At larger scales, Terraform’s metered, per-resource pricing increases linearly, making long-term costs less predictable. In contrast, Firefly’s pricing remains stable and predictable until organizations move into custom enterprise tiers.
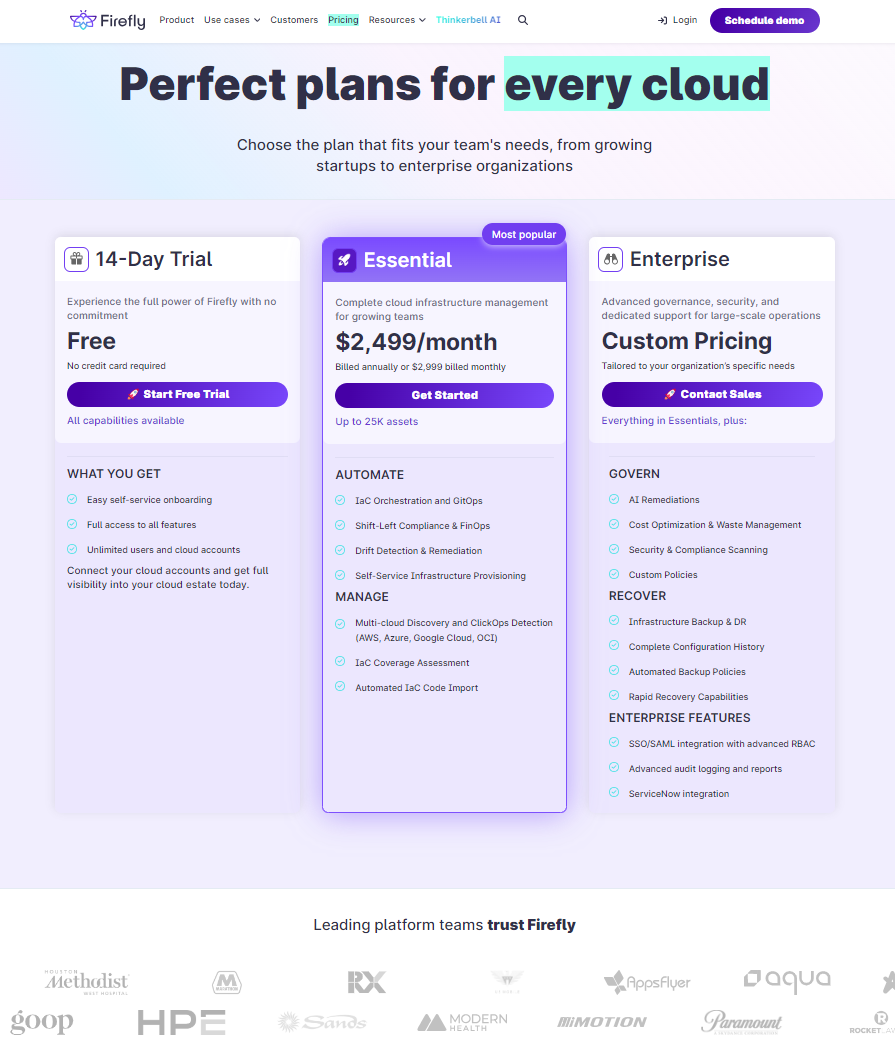
Below is Firefly’s official pricing, with a more detailed breakdown:
Firefly can run alongside existing Terraform deployments or serve as the central control layer for infrastructure visibility, governance, and cost management. For teams looking to simplify operations and reduce tooling overhead as they scale infrastructure, it offers an alternative to combining multiple Terraform Cloud tiers and third-party plugins.
FAQs
Does Terraform Cloud have a free tier?
Yes, but it's limited. The free tier supports up to 500 managed resources and one concurrent run. It includes basic VCS integration and remote state storage, but no policy enforcement, SSO, or advanced governance features. Many teams outgrow it quickly, especially when managing multi-env setups or modular infrastructure.
What is the resource limit in Terraform Cloud?
Limits vary by tier. The free tier caps at 500 managed resources. Paid tiers charge per resource: Essentials ($0.10/resource/month), Standard ($0.47), Premium ($0.99). There's no hard upper bound, but cost scales linearly with resource count, and concurrency is capped (e.g., 3 concurrent runs on Standard, 10 on Premium). For large environments, this creates real operational bottlenecks.
Can I use Terraform without Terraform Cloud?
Yes. You can use Terraform open source (CLI) with your own CI pipelines and remote backends like S3, GCS, or Azure Blob Storage. Many teams prefer this for flexibility and cost control. Terraform Cloud adds a managed UI, concurrency control, and policy hooks ,but they’re optional if you’re willing to manage the workflow yourself.
Why are people moving away from Terraform Cloud?
Most teams aren’t abandoning Terraform as a tool; they’re reconsidering Terraform Cloud as the control plane due to:
- Per-resource pricing (RUM) that inflates quickly at scale
- Limited concurrency, even on paid tiers
- Policy enforcement and governance are paywalled behind Premium+
- Lack of drift detection or cost visibility out of the box
Many teams hit scaling friction and start looking at open source alternatives, self-hosted setups, or complementary tools to regain visibility and control without spiking costs.













.png)


.webp)


.webp)















